![]() Brandon Lee  security, windows, windows 10 3
Brandon Lee  security, windows, windows 10 3
NetBIOS was initially created to allow applications to communicate without understanding the details of the network, including error recovery. It operates at the session layer, layer 5 of the OSI model. As with other legacy technologies, the main reason for disabling NetBIOS is security. There are two ways to achieve this goal: via either DHCP or a registry key.
Contents
- Reasons to disable NetBIOS
- Considerations before disabling
- Disabling NetBIOS in your network
- Conclusion
- Author
- Recent Posts
Brandon Lee has been in the IT industry 15+ years and focuses on networking and virtualization. He contributes to the community through various blog posts and technical documentation primarily at Virtualizationhowto.com.
Latest posts by Brandon Lee (see all)
- Install vCenter 8 in VMware Workstation - Tue, Jan 10 2023
- Install ESXi in a VirtualBox VM - Tue, Dec 27 2022
- Self-service password reset with ManageEngine ADSelfService Plus - Wed, Dec 21 2022
The original NetBIOS implementations used a frame provided by NetBEUI, since NetBIOS is not a network protocol itself. Most commonly, it is still in use in enterprise networks with NetBIOS over TCP/IP (NBT). TCP/IP networks overcame the limitation of NetBEUI not being routable. NetBIOS is only supported on IPv4 networks and is not compatible with IPv6.
NetBIOS offers three main capabilities:
- Name resolution—TCP or UDP over port 137 provides name resolution and registration services.
- Datagram services—UDP port 138 allows for broadcasts to all computers on the network and provides connectionless communication, such as error reporting.
- Session services—TCP port 139 provides the communication channel, allowing two computers to communicate.
Even though NetBIOS was developed in the 1980s, amazingly, you can still see that it is alive and well in Windows 10 today.
Reasons to disable NetBIOS
NetBIOS is a relic of legacy network technology and is often part of the technical debt and legacy infrastructure left behind after upgrading applications and other technologies. In addition, the network is generally one of the slowest areas of infrastructure that is changed. As a result, organizations may still have legacy network protocols and services enabled if these are needed for compatibility.
There are good reasons to disable NetBIOS. However, arguably, the main reason that many businesses may start looking at disabling NetBIOS is security. Attackers look for any weakness in the infrastructure, network, or other environmental components, providing a means for compromise.
As described earlier, NetBIOS uses the NBT protocol. NBT is vulnerable to poisoning attacks because it is not an authenticated protocol. A skilled hacker can impersonate or spoof the identity of NBT frames and misdirect traffic on the network, allowing sensitive information to be stolen. This may include the NTLM hash of end user credentials transmitted by the user's computer.
It is also recommended to disable NetBIOS over TCP/IP to improve network performance. Disabling NetBIOS over TCP/IP is especially recommended on Hyper-V and Windows Server cluster hosts with dedicated NICs used for traffic, such as iSCSI and Live Migration.
Considerations before disabling
As with any infrastructure or network change, IT admins need to discover whether NetBIOS is actively used in their environments before disabling it. Organizations need to ensure that there are no legacy applications or clients that depend on NetBIOS to function properly. In addition, the DNS infrastructure needs to be implemented correctly and validated for consistency and accuracy before turning off NetBIOS.
It is also a good idea to use a tool like Wireshark to make sure no NetBIOS traffic is observed on the network. This helps validate the actual traffic and find any unknown or hidden dependencies on NetBIOS.
You can also use nbtstat in Windows to view entries in cache and other options.
Disabling NetBIOS in your network
There are a couple of ways that we can effectively disable NetBIOS on a Windows machine. As many organizations use a Windows Server DHCP server, NetBIOS can be controlled using a scope option. Open the DHCP management console using the command dhcpmgmt.msc. Navigate to your DHCP scope and select Scope Options > Configure Options.
Select the Advanced tab. In the Vendor class drop-down box, select Microsoft Windows 2000 Options. Then select the checkbox next to the 001 Microsoft Disable Netbios Option. To disable NetBIOS, in the Data entry field, enter 0x2. All new leases will receive the new scope option.
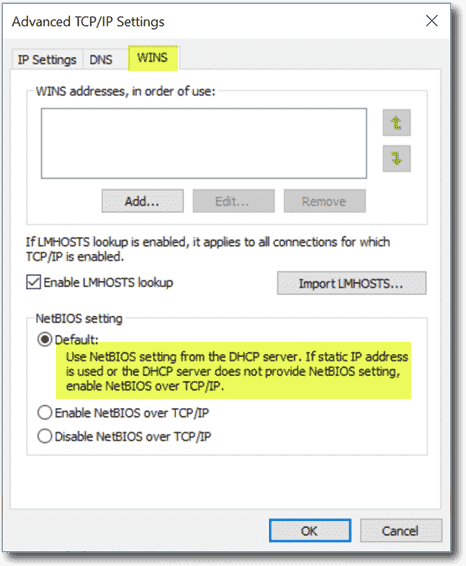
From the client side, Windows 10 has the corresponding setting enabled by default to obtain NetBIOS settings from the DHCP server. Note that under the WINS tab of the Advanced TCP/IP Settings for a network connection in Windows 10, the option selected by default for NetBIOS setting is:
- Use NetBIOS setting from the DHCP server. If static IP address is used or the DHCP server does not provide NetBIOS setting, enable NetBIOS over TCP/IP.
So, if your DHCP server sends a configuration for NetBIOS, Windows 10 will use the setting provided by DHCP.
You can also disable NetBIOS using the Windows registry, as follows:
- Start the registry editor (regedit.exe).
- Open HKLM\SYSTEM\CurrentControlSet\services\NetBT\Parameters\Interfaces.
- Select the corresponding network adapter GUID. To find your corresponding network adapter GUID, start the Wired Autoconfig Windows service (if not running), and run the following command: netsh lan show interfaces.
- GUIDs with the NetbiosOptions value can be set to 0 (uses NetBIOS setting from the DHCP server) or 1 (enables NetBIOS over TCP/IP). To disable, set the option to 2.
- Close the registry editor.
Conclusion
NetBIOS is a network service that has been around for decades now. As many organizations may have migrated from legacy apps and have a proper DNS configuration for name resolution, NetBIOS may be disabled. However, proper auditing and discovery of all applications and dependencies need to be validated.
Subscribe to 4sysops newsletter!
As shown, the DHCP Server can be used to configure DHCP client NetBIOS settings. IT admins can also use the Windows registry to disable NetBIOS.
Related Articles
Find the source of AD account lockouts
 Surender Kumar  active directory, security 2
Surender Kumar  active directory, security 2 In a previous post, we discussed how to quickly unlock AD accounts with PowerShell. However, the main problem admins...
Unlock AD accounts with PowerShell
 Surender Kumar  security, active directory, powershell 0
Surender Kumar  security, active directory, powershell 0 IT admins or helpdesk teams often use graphical tools, such as Active Directory Users and Computers (ADUC), to unlock...
Privacy: Disable cloud-based spell checker in Google Chrome and Microsoft Edge
 Wolfgang Sommergut  security, browser 1
Wolfgang Sommergut  security, browser 1 In addition to the simple, purely local spell checker, the two Chromium-based web browsers, Google Chrome and Microsoft Edge,...
PsLoggedOn: View logged-on users in Windows
 Leos Marek  commands, security 9
Leos Marek  commands, security 9 PsLoggedOn, a command line tool that is part of the Sysinternals suite, gets information about users logged on to...
Controlled folder access: Configure ransomware protection with Group Policy and PowerShell
 Wolfgang Sommergut  security, group policy 0
Wolfgang Sommergut  security, group policy 0 Controlled folder access prevents suspicious programs from modifying or creating files in protected directories, such as Documents, Pictures, Favorites,...
Self-service password reset with ManageEngine ADSelfService Plus
 Brandon Lee  security, active directory, password 1
Brandon Lee  security, active directory, password 1 ManageEngine ADSelfService Plus is a fully featured solution to easily implement self-service password reset, SSO, password synchronization, MFA, and...
Find Active Directory accounts configured for DES and RC4 Kerberos encryption
 Wolfgang Sommergut  security, active directory, encryption 0
Wolfgang Sommergut  security, active directory, encryption 0 While DES has long been considered insecure, CVE-2022-37966 accelerates the departure of RC4 for the encryption of Kerberos tickets....
If a Windows service hangs, restart the service with PowerShell
 Emanuel Halapciuc  processes, powershell, windows 3
Emanuel Halapciuc  processes, powershell, windows 3 That a Windows service hangs (that is, becomes unresponsive or fails to stop) is a common issue admins face....
List Windows processes with PsList
 Leos Marek  processes, security 0
Leos Marek  processes, security 0 PsList is a command line tool that is part of the Sysinternals suite. It allows you to list Windows...
Smart App Control: Protect Windows 11 against ransomware
 Brandon Lee  security 0
Brandon Lee  security 0 Smart App Control is a new security solution from Microsoft built into Windows 11 22H2. It aims to add...
Encrypt email in Outlook with Microsoft 365
 Robert Pearman  encryption, security, cloud computing, microsoft 365 0
Robert Pearman  encryption, security, cloud computing, microsoft 365 0 A support ticket came in recently, in which a client asked whether they needed to upgrade their Microsoft 365...
Enable TLS on SQL Server
 Surender Kumar  encryption, security, database 0
Surender Kumar  encryption, security, database 0 Secure Socket Layer (SSL) and Transport Layer Security (TLS, which builds on the now deprecated SSL protocol) allow you...
Restricting registration to Azure AD MFA from trusted locations with Conditional Access policy
 Robert Pearman  security, cloud computing, azure 0
Robert Pearman  security, cloud computing, azure 0 You may be familiar with the Conditional Access policy feature in Azure AD as a means to control access...
Azure AD MFA with number matching and temporary access passes
 Robert Pearman  security, cloud computing, azure 0
Robert Pearman  security, cloud computing, azure 0 Microsoft will enable the new number matching feature by default in February 2023. Number matching for Azure AD MFA...
Microsoft 365 compliance policy: Control access with compliant devices
 Robert Pearman  security, cloud computing, microsoft 365 0
Robert Pearman  security, cloud computing, microsoft 365 0 With the procedure described in this post, you can ensure that only devices with an assigned Microsoft 365 compliance...
When did users last change their password in Active Directory?
 Wolfgang Sommergut  password, active directory, security 0
Wolfgang Sommergut  password, active directory, security 0 Changing passwords regularly is no longer recommended, and the Security Baseline for Windows doesn't include a corresponding setting. Nevertheless,...
Active Directory passwords: All you need to know
 Surender Kumar  password, active directory, security 5
Surender Kumar  password, active directory, security 5 All Windows administrators need to know the essential concepts of Active Directory passwords: how passwords are stored in Active...
Configuring Defender Exploit Guard network protection
 Wolfgang Sommergut  antivirus, security, defender 0
Wolfgang Sommergut  antivirus, security, defender 0 One of the features of Defender Exploit Guard is network protection. It blocks communication with dangerous domains or IP...
Disable UAC with Group Policy and set PIN in Windows Hello
 Brandon Lee  group policy, security, windows 0
Brandon Lee  group policy, security, windows 0 User Account Control helps to implement proper permission levels for users accessing systems. Instead of needing administrator privileges, UAC...
Windows 10 22H2: New Group Policy settings and updated Security Baseline, no ADK
 Wolfgang Sommergut  group policy, active directory, windows 0
Wolfgang Sommergut  group policy, active directory, windows 0 Microsoft released version 22H2 of Windows 10 (Windows 10 2022 Update). It offers practically no new features for end...
3 Comments
Samir 1 year ago
Was so much easier to remove it when it was a separate protocol stack and not part of the tcp/ip configuration. I wonder if there are any drawbacks to still running IPX today?
Peter 1 year ago
Thanks for the interesting article.
Maybe a useful follow-up article would be tools to do a network audit on what is using NetBIOS.Thanks